
Digital integrity forms the baseline of our modern economic system, yet a highly calibrated Facebook verification scam is currently undermining this foundation. Security researchers recently identified a massive phishing operation that exploits the high demand for social media credibility. Consequently, over 30,000 accounts have already fallen victim to this strategic exploitation of user trust.
The Mechanics of Structural Exploitation
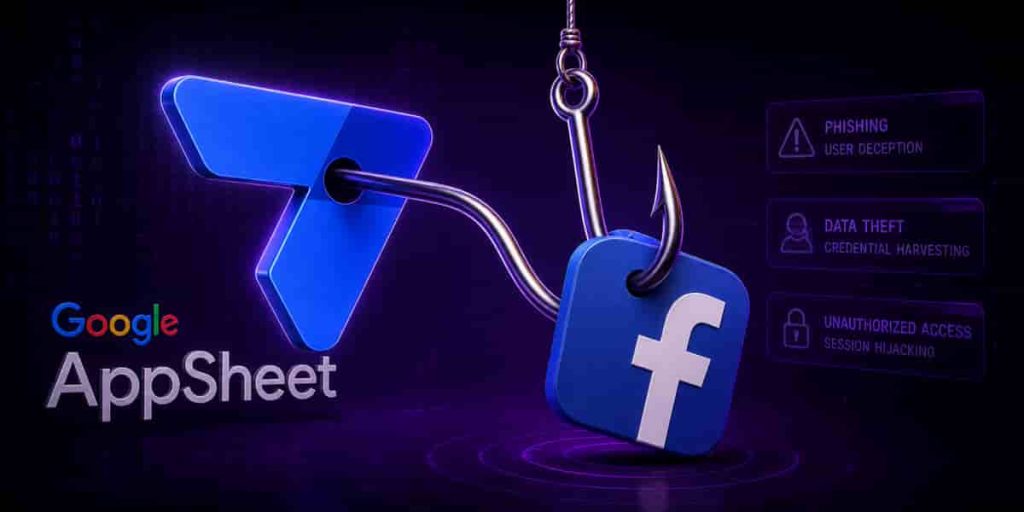
The attackers deploy a precision-based tactic by utilizing legitimate systems to bypass standard security protocols. Specifically, the group misuses Google AppSheet to send notification emails that appear entirely authentic to the recipient. Because these communications originate from a trusted Google domain, most email filters fail to flag them as malicious. This structural flaw allows the phishing campaign to reach the primary inboxes of high-value targets, including creators and corporate entities.
Tactical Diversification in Phishing
- Verification Lures: Offering “free” blue ticks without the standard Meta subscription requirement.
- Fear-Based Prompts: Threatening immediate account suspension due to alleged copyright violations.
- Bypass Techniques: Using invisible characters in email addresses to evade automated detection systems.
The Situation Room: Analysis
The Translation
This is not a traditional “Nigerian Prince” email; it is a sophisticated institutional exploit. The attackers are not hacking Facebook’s servers directly. Instead, they are “spoofing” the authority of Google’s infrastructure to steal your login credentials. By mimicking the official verification process—complete with CAPTCHAs—they create a psychological environment of legitimacy that tricks even tech-savvy users into surrendering two-factor authentication codes.

The Socio-Economic Impact
For the Pakistani professional or small business owner, a hijacked account represents more than just lost photos; it is a loss of digital capital. These compromised accounts are often resold by Vietnam-based syndicates to spread misinformation or conduct further financial fraud. In a growing digital economy like Pakistan, such breaches disrupt the “trust-coefficient” necessary for e-commerce and digital entrepreneurship to thrive.
The Forward Path (Opinion)
This development represents a significant Momentum Shift in cybercrime sophistication. We are moving away from brute-force attacks toward high-precision social engineering. Users must adopt a “Zero Trust” baseline for all unsolicited communications. Verification of any account status should only occur through the official Meta Business Suite or the native settings menu, bypassing all external email links entirely.








